Linux System Administration: Empowering the Digital Infrastructure
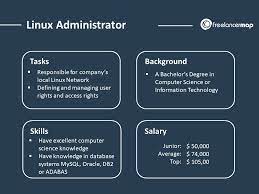
In the ever-evolving landscape of technology, Linux has emerged as a powerful and versatile operating system that has revolutionized the way we manage and administer digital infrastructure. Linux system administration encompasses a range of tasks, from setting up and configuring servers to ensuring smooth operations and security. In this article, we will delve into the world of Linux system administration and explore its significance in today’s digital age.
At its core, Linux is an open-source operating system that provides a solid foundation for building robust and scalable infrastructures. Its flexibility allows administrators to tailor their systems to meet specific requirements, making it a popular choice for everything from small businesses to large enterprises. With its vast array of distributions such as Ubuntu, CentOS, and Debian, Linux offers a diverse ecosystem that caters to different needs.
One of the key strengths of Linux lies in its command-line interface (CLI), which empowers administrators with granular control over their systems. This interface provides access to a wide range of powerful tools and utilities that enable efficient management of resources, user accounts, file systems, network configurations, and more. By leveraging the CLI, administrators can automate repetitive tasks through scripts or utilize configuration management tools like Ansible or Puppet to ensure consistency across multiple systems.
Security is paramount in any digital infrastructure, and Linux excels in this area. With its strong focus on stability and robustness, combined with regular security updates from the open-source community, Linux provides a secure foundation for critical applications and services. Administrators can implement various security measures such as firewalls, intrusion detection systems (IDS), access controls, encryption protocols, and more to safeguard their systems against threats.
Linux also offers extensive networking capabilities that make it an ideal choice for managing network services such as web servers (Apache/Nginx), database servers (MySQL/PostgreSQL), mail servers (Postfix/Exim), DNS servers (Bind/PowerDNS), and many others. Administrators can configure and optimize these services to ensure high availability, scalability, and performance, enabling seamless communication and collaboration within the digital infrastructure.
Moreover, Linux system administration embraces the principles of automation and monitoring. Administrators can leverage tools like Nagios, Zabbix, or Prometheus to monitor system health, resource usage, network traffic, and application performance. By proactively identifying bottlenecks or anomalies, administrators can take timely action to prevent potential issues or optimize system performance.
The Linux community plays a vital role in the world of system administration. With an active and passionate community of developers, administrators can access a wealth of knowledge through forums, mailing lists, and online resources. The collaborative nature of the community fosters continuous improvement and innovation in Linux administration practices.
In conclusion, Linux system administration is a crucial discipline that empowers organizations to build robust and secure digital infrastructures. With its flexibility, stability, security features, networking capabilities, automation tools, and vibrant community support, Linux provides administrators with the tools they need to effectively manage their systems. By embracing Linux as their operating system of choice for administration tasks, organizations can unlock new levels of efficiency and reliability in their digital operations.
Whether you are a seasoned administrator or just starting your journey in Linux system administration, there is always something new to learn and explore. Embrace the power of Linux and join the ever-growing community of professionals who are shaping the future of digital infrastructure management.
Advantages of Linux System Administration: Security, Affordability, Customizability, Reliability, and Scalability
- Security
- Cost
- Customization
- Reliability
- Scalability
Challenges in Linux System Administration: GUI Absence, Complexity, and Security Risks
- Lack of GUI
- Complexity
- Security Risks
Security
Security: Linux’s Fortress of Protection for Sensitive Data
When it comes to safeguarding sensitive data, Linux system administration stands tall as a bastion of security. Linux has earned a well-deserved reputation for its robust security features, making it the go-to choice for system administrators who prioritize data protection. In this article, we will explore how Linux’s security prowess enhances the role of system administrators in ensuring the safety and integrity of valuable information.
Linux’s foundation lies in its open-source nature, which allows a vast community of developers to continuously scrutinize and improve its code. This collaborative effort ensures that vulnerabilities are swiftly identified and patched, making Linux inherently resilient against cyber threats. System administrators benefit from this collective vigilance, as they can rely on a stable and secure operating system to protect sensitive data.
One of the key strengths of Linux lies in its strict access controls. The operating system grants administrators granular control over user permissions and privileges, enabling them to restrict access to critical files and directories. This prevents unauthorized users from tampering with or accessing sensitive data, reducing the risk of data breaches or leaks.
Moreover, Linux offers robust encryption mechanisms that shield data both at rest and in transit. Administrators can employ tools like GNU Privacy Guard (GPG) or OpenSSL to encrypt files and communications, rendering them unreadable to anyone without the proper decryption keys. By implementing encryption protocols effectively, system administrators add an extra layer of protection against potential threats.
Linux also boasts powerful firewalls and network security tools that fortify digital infrastructures against external attacks. System administrators can configure firewalls like iptables or nftables to filter network traffic based on predefined rules, ensuring only authorized connections are allowed. Additionally, intrusion detection systems (IDS) such as Snort or Suricata actively monitor network activities for suspicious behavior, providing early warnings about potential security breaches.
In addition to these built-in security features, Linux benefits from an extensive range of security-focused software and utilities. Administrators can leverage tools like SELinux (Security-Enhanced Linux) or AppArmor to enforce mandatory access controls, further restricting the actions of users and applications. Additionally, Linux offers a wide selection of security auditing tools, such as AIDE or Lynis, which assist administrators in performing regular vulnerability assessments and system hardening.
The Linux community plays a vital role in maintaining the security of the operating system. With its active and knowledgeable members, the community provides constant support and shares best practices for securing Linux systems. Administrators can tap into this wealth of expertise through online forums, mailing lists, and dedicated security communities, allowing them to stay up-to-date with the latest security trends and techniques.
In conclusion, Linux’s robust security features make it an ideal choice for system administrators tasked with protecting sensitive data. From strict access controls to encryption mechanisms, powerful firewalls to network security tools, Linux equips administrators with a comprehensive toolkit to fortify digital infrastructures against potential threats. By embracing Linux system administration, organizations can establish a secure environment that safeguards valuable information from malicious actors.
As cyber threats continue to evolve in sophistication, system administrators must remain vigilant in their efforts to protect sensitive data. By harnessing the power of Linux’s security features and staying engaged with the vibrant community, administrators can confidently navigate the ever-changing landscape of cybersecurity while ensuring the safety and integrity of their organization’s most valuable assets.
Cost
The Cost Advantage of Linux System Administration
In the realm of system administration, one significant advantage that Linux brings to the table is its cost-effectiveness. Unlike many other operating systems, Linux is free and open source, making it an appealing choice for businesses of all sizes. In this article, we will explore how the cost advantage of Linux system administration can benefit organizations in various ways.
One of the most obvious benefits of Linux’s free and open-source nature is that there are no licensing fees associated with its usage. This means that businesses can deploy Linux on their servers and workstations without incurring any additional costs for operating system licenses. Whether you are a startup with limited resources or a large enterprise managing a vast infrastructure, the absence of licensing fees can significantly reduce your IT expenses.
The cost savings extend beyond just the initial deployment. With Linux, businesses have access to a vast repository of free and open-source software applications that can be seamlessly integrated into their systems. From web servers to databases, office suites to content management systems, there are numerous high-quality software options available at no cost. This allows organizations to build robust infrastructures without having to invest heavily in proprietary software licenses.
Furthermore, as Linux is an open-source platform, it encourages collaboration and innovation within the community. A global network of developers actively contributes to improving and expanding the capabilities of Linux-based systems. This means that businesses can leverage these advancements without having to pay for expensive upgrades or feature enhancements typically associated with proprietary software.
Another aspect where Linux shines in terms of cost-effectiveness is its hardware requirements. Linux has a reputation for being lightweight and efficient, allowing it to run smoothly on older or less powerful hardware configurations. This means that businesses can extend the lifespan of their existing infrastructure by utilizing Linux as their operating system, thus avoiding costly hardware upgrades.
Moreover, the absence of licensing fees and lower hardware requirements also translates into reduced maintenance costs. With fewer financial obligations tied to the operating system, businesses can allocate their resources towards other critical areas of their IT infrastructure, such as security measures, backup solutions, or employee training.
It is important to note that while Linux itself is free, organizations may choose to invest in professional support services or enterprise-grade distributions for enhanced technical assistance and additional features. However, even with these optional expenses factored in, Linux remains a cost-effective option compared to proprietary alternatives.
In conclusion, the cost advantage of Linux system administration is a compelling reason for businesses to consider adopting this open-source operating system. By eliminating licensing fees and offering a vast array of free software options, Linux provides organizations with significant cost savings. Additionally, its lightweight nature and ability to run on older hardware further contribute to reduced expenses in terms of hardware upgrades and maintenance. Embracing Linux as a system administrator not only ensures financial efficiency but also empowers businesses with a reliable and flexible platform for their digital infrastructure needs.
Customization
Customization: Unleashing the Power of Linux System Administration
One of the standout advantages of Linux system administration is its unparalleled flexibility and customization capabilities. Unlike proprietary operating systems, Linux empowers system administrators to tailor their systems to meet their specific needs and requirements. This level of customization is a game-changer in the world of digital infrastructure management.
Linux provides a vast array of distributions, each with its own set of features and configurations. Whether it’s Ubuntu, CentOS, Debian, or any other distribution, administrators have the freedom to choose the one that best suits their environment. This flexibility allows for seamless integration with existing infrastructure and ensures compatibility with a wide range of hardware and software.
Once a distribution is selected, administrators can dive into the heart of Linux system administration: the command-line interface (CLI). The CLI offers an extensive suite of tools and utilities that enable fine-grained control over various aspects of the system. From configuring network settings to managing user accounts and permissions, administrators can customize every aspect to align with their organization’s unique requirements.
The ability to customize extends beyond basic configurations. Linux allows administrators to install only what they need, avoiding unnecessary bloatware that can slow down systems or introduce security vulnerabilities. This level of control not only optimizes performance but also enhances security by reducing the attack surface.
Moreover, Linux offers robust package management systems such as APT (Advanced Package Tool) or YUM (Yellowdog Updater Modified), which streamline software installation and updates. Administrators can cherry-pick specific packages or libraries required for their applications, ensuring efficient resource utilization without unnecessary overhead.
Another aspect where customization shines is in desktop environments. Linux offers a wide range of desktop environments such as GNOME, KDE Plasma, Xfce, and more. Administrators can choose an environment that best suits their preferences or those of end-users. By tailoring the desktop environment’s appearance and functionality, productivity can be enhanced while providing a familiar and intuitive user experience.
Furthermore, Linux’s open-source nature encourages collaboration and innovation. Administrators can tap into the vast Linux community, which is brimming with developers, enthusiasts, and experts. This collective knowledge allows administrators to access a wealth of resources, tips, and solutions to address specific challenges or explore new possibilities for customization.
The flexibility of Linux system administration not only empowers administrators but also benefits organizations as a whole. By customizing systems to align with specific needs, businesses can optimize workflows, improve efficiency, and reduce costs. Whether it’s configuring server settings for optimal performance or tailoring desktop environments for enhanced productivity, Linux provides the tools needed to create an infrastructure that works seamlessly with the organization’s unique requirements.
In conclusion, customization is a standout pro of Linux system administration. The ability to tailor systems according to specific needs and requirements sets Linux apart from other operating systems. From choosing the right distribution to fine-tuning configurations and desktop environments, administrators have unparalleled control over their digital infrastructure. Embracing the power of customization in Linux system administration unlocks endless possibilities for organizations seeking optimized performance, enhanced security, and tailored user experiences.
Reliability
Reliability: Linux, the Trustworthy Foundation for Businesses
In the fast-paced world of business, reliability is key. This is where Linux system administration shines, offering a robust and dependable platform for businesses of all sizes. One of the primary strengths of Linux lies in its open-source nature, which ensures constant updates and improvements by a global community of dedicated developers. Let’s explore how this reliability factor sets Linux apart as an ideal choice for businesses.
The open-source nature of Linux means that its source code is freely available to anyone. This fosters a collaborative environment where developers from around the world can contribute their expertise and insights to enhance the operating system. As a result, Linux benefits from continuous updates and improvements, ensuring that it remains at the forefront of technology.
With each update, potential vulnerabilities are identified and promptly addressed by the community. The collective effort of these developers helps fortify Linux’s security measures, making it a reliable platform for businesses seeking to protect their sensitive data and digital assets. Regular security patches keep pace with emerging threats, reducing the risk of breaches or disruptions to critical operations.
Furthermore, Linux’s reliability stems from its stability and performance. The rigorous testing processes that accompany each release ensure that it meets high standards before reaching end-users. The open-source community actively participates in bug identification and resolution, resulting in a stable operating system with fewer crashes or unexpected downtime.
Businesses can also benefit from Linux’s scalability. Whether an organization is just starting out or experiencing rapid growth, Linux offers flexibility in terms of resource allocation and system expansion. Administrators can easily adapt their infrastructure to meet changing demands without compromising performance or stability.
Moreover, Linux’s reliability extends beyond its core functionality. The vast array of available software packages allows businesses to tailor their systems according to specific needs. From web servers to database management systems and productivity tools, there are numerous options available within the Linux ecosystem. This versatility ensures that businesses can find suitable solutions for their unique requirements, further enhancing reliability and productivity.
The reliability of Linux is not just limited to large enterprises. Small and medium-sized businesses can also benefit from its stability and performance. Linux’s cost-effectiveness, coupled with its robustness, makes it an attractive choice for organizations with limited resources. By leveraging Linux system administration, businesses can optimize their operations without incurring hefty licensing fees associated with proprietary software.
In conclusion, the reliability of Linux system administration is a compelling reason for businesses to embrace this open-source operating system. The constant updates and improvements driven by a global community of developers ensure that Linux remains a dependable platform for organizations seeking stability, security, and scalability. By harnessing the power of Linux, businesses can build a solid foundation for their digital infrastructure and confidently navigate the ever-changing landscape of technology.
Choose Linux system administration as your gateway to a reliable and efficient business environment. Embrace the open-source philosophy and unlock the potential that Linux offers to propel your business forward.
Scalability
Scalability: Empowering Linux System Administration
In the realm of system administration, scalability is a crucial factor that determines the ability to adapt and grow with changing needs. Linux, with its modular design, offers unparalleled scalability for system administrators, allowing them to effortlessly scale up or down their infrastructure as required. This pro of Linux system administration provides administrators with the flexibility and agility they need in today’s dynamic digital landscape.
The modular design of the Linux operating system is one of its defining features. Unlike monolithic systems where components are tightly integrated, Linux adopts a modular approach that allows administrators to add or remove components seamlessly. This means that as an organization’s requirements evolve, administrators can easily expand their infrastructure by adding new components or services without disrupting existing operations.
The ease and speed at which components can be added or removed in Linux make it an ideal choice for scaling systems. Administrators can quickly adapt to increased workloads by adding more servers, storage devices, or network resources. By doing so, they ensure that their infrastructure remains responsive and efficient even under heavy loads.
Conversely, when there is a need to downscale due to changing demands or cost optimization, Linux enables administrators to remove unnecessary components without affecting the overall stability of the system. This flexibility allows organizations to allocate resources effectively and avoid unnecessary expenses associated with over-provisioning.
Moreover, scalability in Linux extends beyond hardware resources. Administrators can easily scale software services by deploying virtualization technologies such as containers or virtual machines. These technologies provide isolation and encapsulation, enabling administrators to create instances of applications or services on-demand. This ability to scale software services independently allows for efficient resource utilization and eliminates the need for dedicated hardware for each service.
The scalability offered by Linux empowers system administrators to adapt their infrastructure rapidly in response to changing business needs. Whether it’s accommodating sudden spikes in traffic, expanding storage capacity, or deploying new services quickly, Linux provides a solid foundation for seamless scalability.
Furthermore, the open-source nature of Linux fosters a vibrant ecosystem of tools and technologies that further enhance scalability. Administrators can leverage orchestration frameworks like Kubernetes or containerization platforms like Docker to automate the deployment and management of scalable applications. These tools simplify the process of scaling services, allowing administrators to focus on strategic initiatives rather than manual configuration tasks.
In conclusion, scalability is a significant pro of Linux system administration. The modular design of Linux empowers administrators with the ability to effortlessly scale their infrastructure up or down as needed, adapting to changing workloads and demands. With its flexibility in adding or removing components, Linux provides a solid foundation for building scalable and responsive systems. Embracing Linux system administration enables organizations to achieve optimal resource utilization, cost efficiency, and adaptability in today’s ever-evolving digital landscape.
Lack of GUI
The Challenge of Command Line: A Con of Linux System Administration
Linux system administration has long been praised for its flexibility, security, and robustness. However, it is important to acknowledge that one of the challenges faced by newcomers to Linux administration is the lack of a graphical user interface (GUI). Unlike some other operating systems, Linux primarily relies on the command line interface (CLI) for system management. While the CLI offers unparalleled control and efficiency, it can be daunting for those who are unfamiliar with it.
For individuals accustomed to a GUI-driven environment, the transition to a CLI-based system can initially feel overwhelming. The reliance on text-based commands and keyboard inputs may seem archaic or complex at first glance. Understanding command syntax, navigating file systems, and executing tasks through commands can be a steep learning curve for beginners.
Moreover, performing routine administrative tasks through the CLI may require memorizing or referencing specific commands and their options. This can be time-consuming and frustrating for those who are accustomed to point-and-click interactions in a GUI environment. Additionally, troubleshooting issues or diagnosing problems effectively often requires a deeper understanding of the underlying system components and their interdependencies.
However, it is worth noting that while the lack of GUI may present challenges initially, it also offers significant advantages in terms of efficiency and flexibility once users become familiar with it. The CLI provides administrators with fine-grained control over their systems and allows for automation through scripting. Furthermore, many powerful tools and utilities are specifically designed for use in the command line environment.
Fortunately, there are resources available to assist those who are new to Linux system administration. Online tutorials, documentation, forums, and communities provide valuable guidance and support for individuals seeking to enhance their CLI skills. Additionally, some distributions offer user-friendly GUI interfaces layered on top of the underlying command line infrastructure to ease the transition for beginners.
In conclusion, while the lack of GUI in Linux system administration may pose an initial challenge for those unfamiliar with the command line interface, it is important to recognize that this aspect also brings significant benefits. With perseverance and dedication, individuals can overcome the learning curve and unlock the power and efficiency that Linux administration offers. By embracing the CLI and leveraging available resources, users can gain proficiency in Linux system administration and reap the rewards of a robust and flexible operating system.
Complexity
Complexity: Unraveling the Challenge of Linux System Administration
While Linux system administration offers a multitude of benefits, it is important to acknowledge that managing a Linux system can sometimes be complex and time-consuming. This complexity arises from the abundance of configuration files and commands that administrators need to navigate. In this article, we will explore this con of Linux system administration and discuss strategies to overcome the challenges it presents.
One of the primary reasons behind the perceived complexity of Linux system administration is the sheer number of configuration files scattered throughout the operating system. These files control various aspects of the system, including network settings, user accounts, software packages, and more. Each file may have its own syntax and structure, requiring administrators to understand and modify them correctly.
Furthermore, Linux offers a vast array of command-line tools for system administration. While these tools provide powerful capabilities, they often come with a steep learning curve. Administrators need to familiarize themselves with numerous commands and their respective options to effectively manage their systems. This can be overwhelming for beginners or those transitioning from other operating systems.
However, it is important to note that complexity does not necessarily equate to impossibility or inefficiency. With proper knowledge and experience, administrators can navigate through this intricacy and streamline their management processes. Here are some strategies to overcome the challenges posed by complexity in Linux system administration:
- Education and Training: Investing time in learning about Linux administration concepts, file structures, and command-line tools is crucial. Online tutorials, documentation resources, forums, and training courses can provide valuable insights into managing a Linux system effectively.
- Automation: Leveraging automation tools such as shell scripts or configuration management systems like Ansible or Puppet can simplify repetitive tasks by reducing manual intervention. By automating routine procedures, administrators can save time and ensure consistency across multiple systems.
- Documentation: Creating comprehensive documentation tailored to your specific environment can serve as a valuable resource for future reference. Documenting configuration changes, troubleshooting steps, and best practices can help streamline future system administration tasks.
- Community Support: The Linux community is known for its collaborative nature and willingness to help. Engaging with the community through forums, mailing lists, or social media platforms can provide insights, solutions, and guidance when faced with challenging administration issues.
- Planning and Testing: Before implementing changes or configurations in a production environment, it is essential to plan and test them in a controlled setting. Setting up a test environment allows administrators to experiment without risking disruption to critical systems.
By adopting these strategies, administrators can effectively navigate the complexity of Linux system administration and harness the full potential of their systems. While initial challenges may arise, the rewards of increased control, security, and customization that Linux offers make it a worthwhile endeavor.
In conclusion, while configuring and managing a Linux system may present complexity due to its numerous configuration files and commands, this challenge can be overcome with knowledge, experience, and the right approach. By embracing continuous learning, automation tools, documentation practices, community support, and careful planning/testing processes, administrators can successfully navigate the intricacies of Linux system administration while reaping its many benefits.
Security Risks
Security Risks in Linux System Administration: Mitigating the Threats
While Linux is renowned for its robust security measures, it is not immune to risks and vulnerabilities. Like any operating system, Linux can be targeted by malicious actors who seek to exploit weaknesses for their own gain. In this article, we will explore the security risks associated with Linux system administration and discuss strategies to mitigate these threats.
One of the primary concerns in Linux system administration is the potential for malware infections. While Linux is generally less susceptible to malware compared to other operating systems, it is not completely immune. Malware specifically designed for Linux environments can still pose a threat if proper precautions are not taken. Administrators must remain vigilant and implement security best practices, such as regularly updating software and using reliable antivirus solutions.
Another aspect of security risks in Linux administration lies in unpatched vulnerabilities. Just like any software, Linux distributions occasionally discover vulnerabilities that need to be patched through updates. Failure to apply these patches promptly can leave systems exposed to potential attacks. Therefore, regular updates are crucial in maintaining a secure environment. Administrators should stay informed about security advisories and promptly apply patches to mitigate known vulnerabilities.
Additionally, improper configuration or weak authentication mechanisms can create opportunities for unauthorized access or privilege escalation. It is essential for administrators to follow best practices when setting up user accounts, permissions, and network configurations. Implementing strong passwords, utilizing secure protocols (e.g., SSH), and employing access controls can significantly reduce the risk of unauthorized access.
Furthermore, third-party software repositories can introduce additional security risks if they are not properly vetted or maintained. Administrators should exercise caution when adding external repositories to their systems and ensure that they come from reputable sources with a track record of maintaining security standards.
To mitigate these security risks effectively, administrators should adopt a multi-layered approach:
- Regularly update software: Keep all system components up-to-date with the latest patches and security fixes to address known vulnerabilities.
- Implement access controls: Enforce strong passwords, implement two-factor authentication where possible, and restrict user privileges to minimize the impact of potential breaches.
- Employ intrusion detection systems (IDS) and log monitoring: Monitor system logs and network traffic for suspicious activities, allowing for early detection and response to potential security threats.
- Utilize firewalls and secure network configurations: Configure firewalls to filter incoming and outgoing traffic, protecting the system from unauthorized access.
- Educate users: Raise awareness among users about best practices for safe computing, including avoiding suspicious emails or websites, practicing good password hygiene, and reporting any security concerns promptly.
- Regularly perform security audits: Conduct periodic assessments of the system’s security posture to identify potential vulnerabilities and take appropriate measures to address them.
While Linux system administration does come with its share of security risks, a proactive approach combined with adherence to best practices can significantly mitigate these threats. By staying informed about emerging vulnerabilities, regularly updating software, implementing strong access controls, and educating users on security practices, administrators can create a robust and secure Linux environment that keeps potential risks at bay.
Remember that no operating system is entirely risk-free; it is the responsibility of administrators to remain vigilant and take appropriate measures to safeguard their Linux systems against evolving threats.